Vault is Pinkfish’s encrypted secret store. It’s where you keep API keys, passwords, tokens, and any other sensitive value that needs to be used from a workflow without being exposed in code or shared via chat. Secrets are encrypted at rest, referenced by ID, and never decrypted client-side. Find it under Tools → Vault.Documentation Index
Fetch the complete documentation index at: https://docs.pinkfish.ai/llms.txt
Use this file to discover all available pages before exploring further.
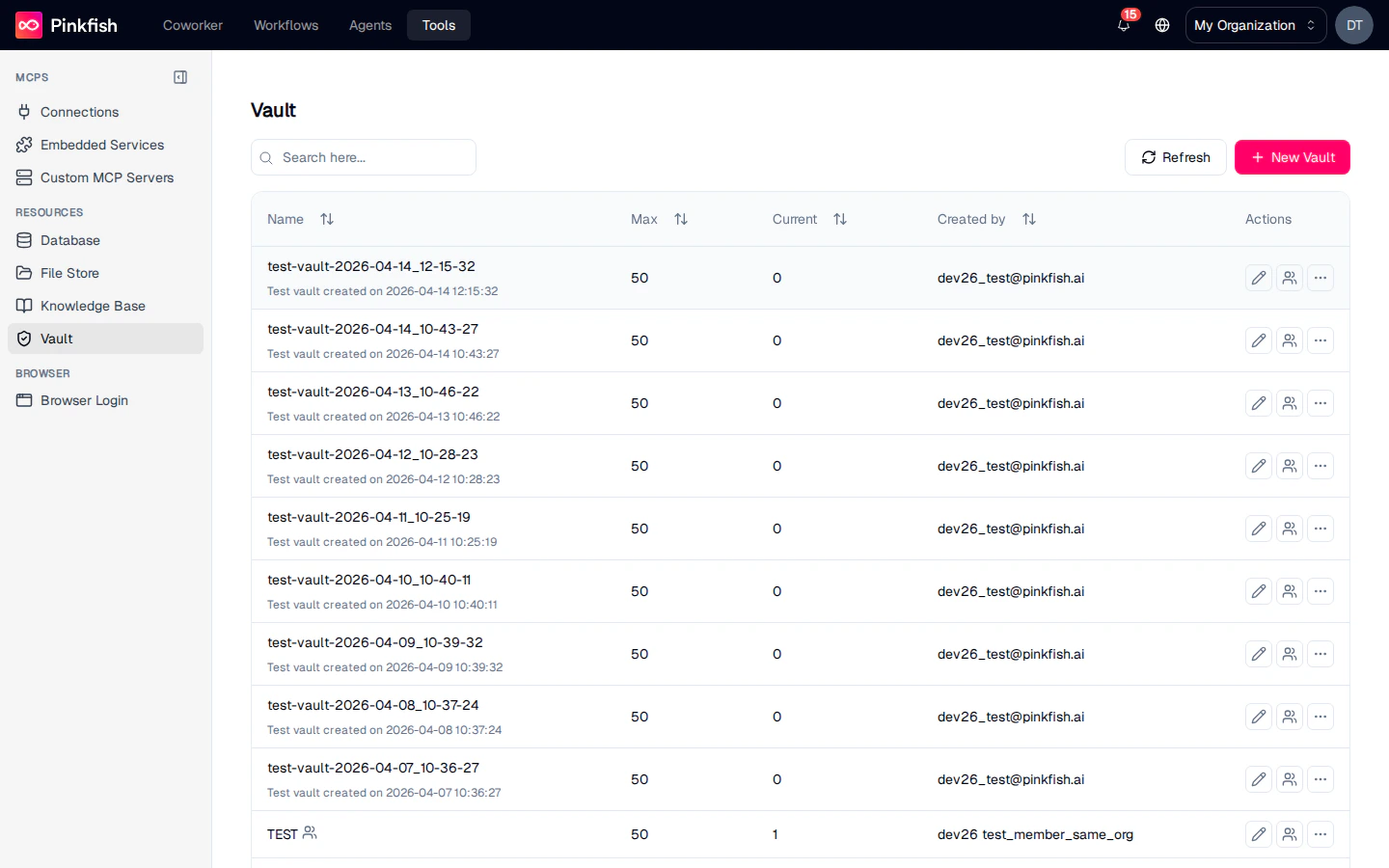
The Vault List
Each row is a vault collection — a logical group of secrets you can share and reference as a unit. Columns mirror the other resource types:| Column | Description |
|---|---|
| Name | Vault collection name. |
| Max | Max secrets allowed in the collection. |
| Current | Current secret count. |
| Created by | Email of the creator. |
| Actions | Share, Rename, More (Delete, Export). |
Inside a Vault Collection
Clicking a row opens the collection.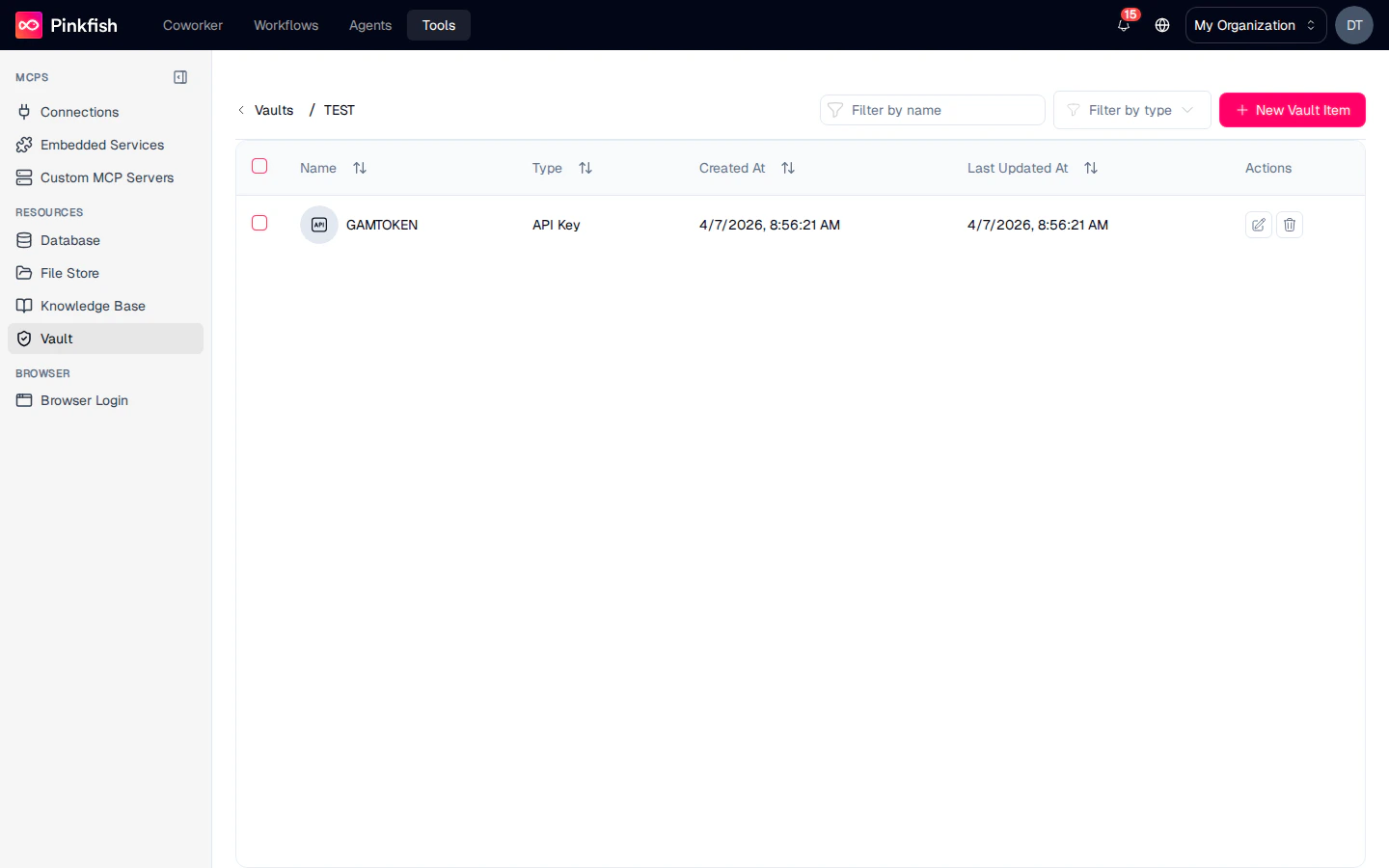
| Button | Action |
|---|---|
| Filter by name | Search by secret name. |
| Filter by type | Filter by Login / API Key / Other. |
| + New Vault Item | Add a new secret. |
| Column | Description |
|---|---|
| Name | Display name (e.g. Stripe Secret Key, GitHub Token, DB Admin). |
| Type | One of Login, API Key, or Other. |
| Created At / Last Updated At | Timestamps. |
| Actions | Edit, Delete. |
Adding a Secret
Click + New Vault Item to open the New Item dialog.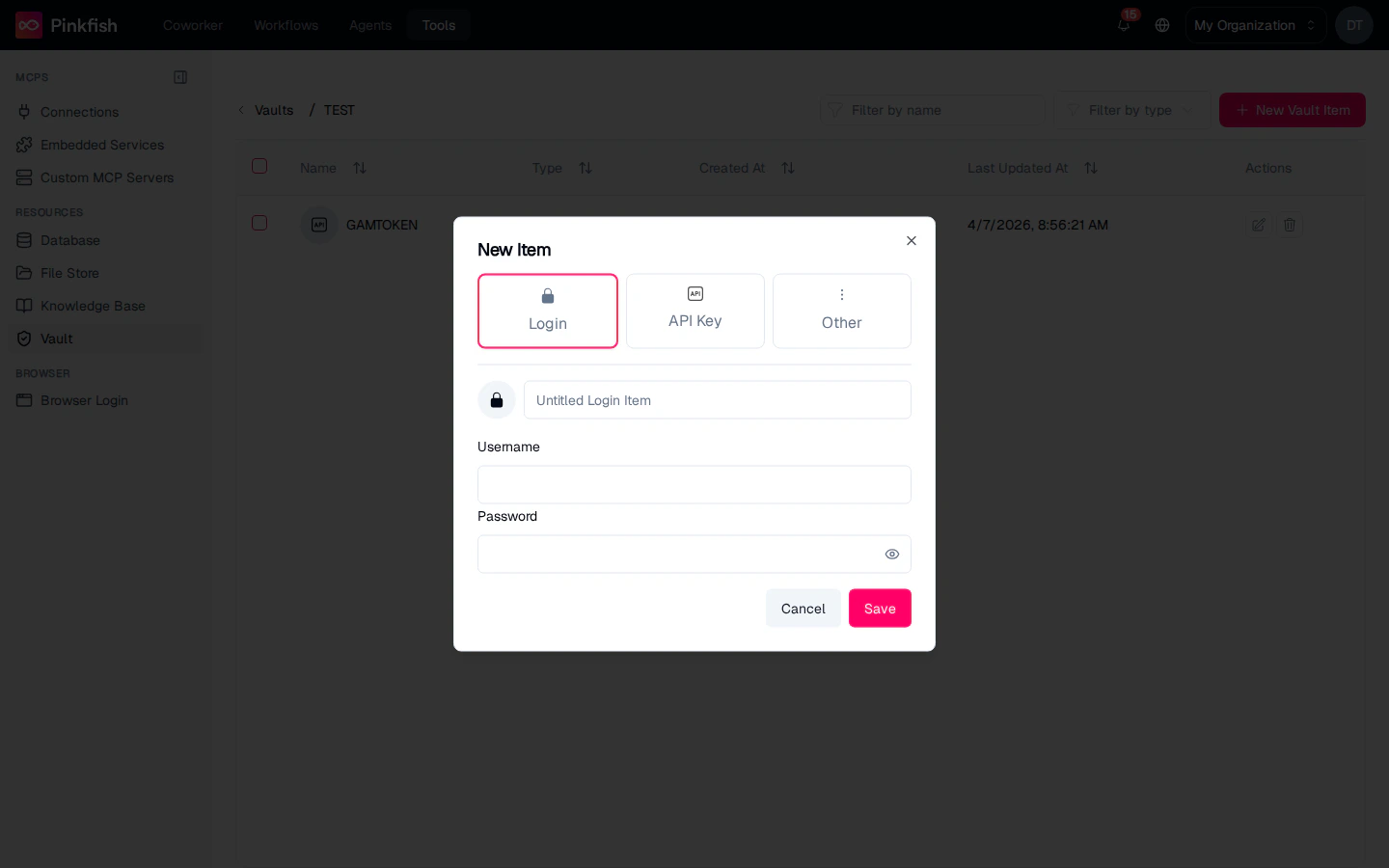
Login
Username + password pairs — for services where your agent signs in as a user.
API Key
Single token or API key — for header-based auth to third-party APIs.
Other
Arbitrary JSON payloads — for multi-field secrets (certificates, connection strings, credential bundles).
Sharing
Vault collections are the most sensitive items on the Tools page, so share them deliberately. The share dialog offers the same ACLs as every other resource:- Read — reference the secret from workflows.
- Write — add, edit, and delete secrets.
- Admin — share with others.
Using Vault Secrets in Workflows
Workflows reference secrets through the/get-secret slash command and the built-in Vault MCP server. The pattern:
- Insert a
/get-secretreference where you’d otherwise hardcode a credential. - At run time, Pinkfish decrypts the value on the server and passes it into the downstream call (HTTP request, database query, etc.).
- The decrypted value never appears in logs, chat history, or workflow outputs.
- Store the API key for a custom integration in a vault and reference it from a scraper workflow.
- Keep DB credentials for an internal tool in a shared vault so multiple workflows can connect without each developer knowing the password.
- Rotate the vault value when a secret expires — every workflow that references it picks up the new value on the next run without changes.
Notes
- Vault is builder-only and requires an eligible plan. When plan access is missing, the Vault entry doesn’t appear in the Tools sidebar at all.
- Secrets are encrypted with per-organization keys and decrypted only within the Pinkfish worker that executes a workflow step. Decrypted values are never written to disk.
- There is no “export secrets” action — secrets can’t be bulk-downloaded, by design.
- For non-sensitive configuration values (feature flags, environment names), use a regular Database collection instead of Vault.

